iSchools and the defense of privacy: A response to Forbes.com
![]()
In this information age of the collection and analysis of massive amounts of data about people by both the private and public sectors, and of social media-supported hate crime, genocide, and attacks on democratic processes, who should help us think about how to protect ourselves? In a recent Forbes.com article titled “Computer Science Could Learn A Lot from Library and Information Science,” Dr. Kalev Leetaru gives an excellent answer: librarians.
He’s right. Let me give you an example. The USA PATRIOT Act was signed into law by President George W. Bush on October 26, 2001. It was swiftly passed by Congress in response to the horrific 9/11 attacks. This act included Section 215, which allowed the government to obtain a secret Foreign Intelligence Surveillance Act (FISA) court order that required third parties to hand over any records or other tangible thing if deemed relevant to an international terrorism counterespionage, or to a foreign intelligence investigation.
The American Library Association (ALA) sounded the alarm about Section 215 and its risk to privacy and to society. The ALA president, Carla Hayden (now the Librarian of Congress), pushed back strongly when the Justice Department claimed that libraries were a logical target of surveillance. Hayden said “libraries are a cornerstone of democracy—where information is free and equally available to everyone. People tend to take that for granted, and they don’t realize what is at stake when that is put at risk.” Her arguments were a rallying cry for civil libertarians, and Section 215 was soon referred to as the “library provision.” Their opposition argued that the risk of terrorism was too high to hamstring the FBI, and in any case, the FISA court judicial review would ensure that civil rights would be protected. In the examples used in these arguments, libraries were often featured.
Libraries were, of course, a proxy argument, and the librarians were right. As we now know, Section 215 was subsequently used by the National Security Agency to secretly collect phone records of millions of Americans. This use was authorized by FISA courts. The disclosure of this program, which is often referred to as PRISM, furthered the erosion in trust many Americans had in their government. According to PEW, only 17 percent of Americans now say they can trust the government in Washington to do what is right at least most of the time. Thirty-seven percent, however, believe libraries contribute “a lot” (and another 37 percent believe they contribute “some”) to helping people decide what information they can trust.
It’s not surprising, perhaps, that we ended up with PRISM. The NSA rightfully wanted to protect Americans, and were strongly motivated to get as much data as possible to do so. A colleague of mine, who worked in the NSA, told me that the PRISM effort was made up of engineers. Engineers are taught to ask what can be done with data. Librarians, on the other hand, are taught to ask what should be done with data.
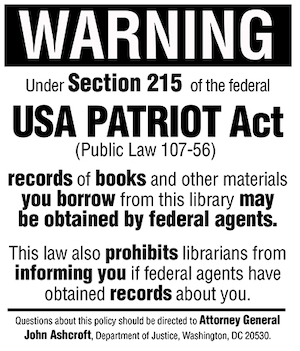
Many libraries posted signs like this, warning patrons about the USA Patriot Act. (Image by Wayne A. Wiegand / American Libraries Magazine)
This is the kernel of Dr. Leetaru’s argument. He says we need more people trained in Library and Information Science (LIS) to inform the people who are developing social media platforms and who are collecting and making use of the massive amounts of data being collected about people. LIS degrees cover topics such as values in design, data minimization, information behavior (including from different historical and cultural viewpoints), cataloging theory, and community informatics. Knowledge like this could help ensure that our evolving information infrastructure protects and promotes civil rights for people and communities.
I’m a dean of a college whose largest graduate program is the Master of LIS (MLIS). I agree with Dr. Leetaru. We need more people trained in LIS topics working with engineers and data scientists in both the public and private sectors. But, I question a claim he makes later in his article:
Sadly, however, as Library and Information Science schools have undergone a wave of rebrandings over the past decade into “iSchools,” this emphasis on data minimization and privacy, use and users of information, community informatics, civil liberties and the human dimension of informational creation and consumption has been steadily eroded in favor of the same harvesting, hoarding, mining and manipulation that were once the exclusive domain of computer science programs.
Our college became an iSchool over a decade ago. There are more than 100 colleges and departments worldwide that identify as iSchools and belong to the iSchools organization. There is considerable diversity among iSchools and the programs that they offer, and it is hard to make generalizations; indeed, not all iSchools came from LIS schools. Some have had an erosion in the interests that Dr. Leetaru mentions, but many have not – including ours. Instead, we have become multidisciplinary, bringing in computer scientists and engineers, sociologists and psychologists, ethnographers and human-computer interaction designers to address the exact problems that Dr. Leetaru points to in his article. We have not run away from LIS values he emphasizes as being needed, but rather broadened the application of them through our educational programs and our research.

Individual with sight impairment using Morphic technology to bring up personal screen reader settings on a computer. (Image provided by the Trace Research & Development Center)
Here are two examples from my college. One large NSF-funded project, called PERVADE, studies how diverse stakeholders (big data researchers, platforms, regulators, and user communities) understand their ethical obligations and choices, and how their decisions impact data system design and use. They have many goals, including developing implementable and sustainable best practices for research ethics. This project is made up of researchers from many communities, including archivists, computer scientists, and socio-technical designers. Another project, called Morphic, focuses on providing ICT access to people facing barriers to the use of computers due to disability, literacy, digital literacy or age. They are already deploying prototype technology, including at my university’s library. A major concern of the project is protecting the privacy of the people using the technology in terms of their disabilities. They have turned down corporate sponsorship because they will not share information about their users with companies, and are even setting up an external Data Ethics Council to oversee privacy after Morphic leaves the University. The Morphic researchers come from accessibility engineering, biomedical and health informatics, computer science, and HCI.
The skills and values taught by LIS programs are even more sharply needed now that information is becoming ever more deeply embedded in our lives. We badly need to bring engineers and computer scientists together with LIS-trained experts to work together. That is what our iSchool, and others like ours, do. We are the library and information science schools for the information age.